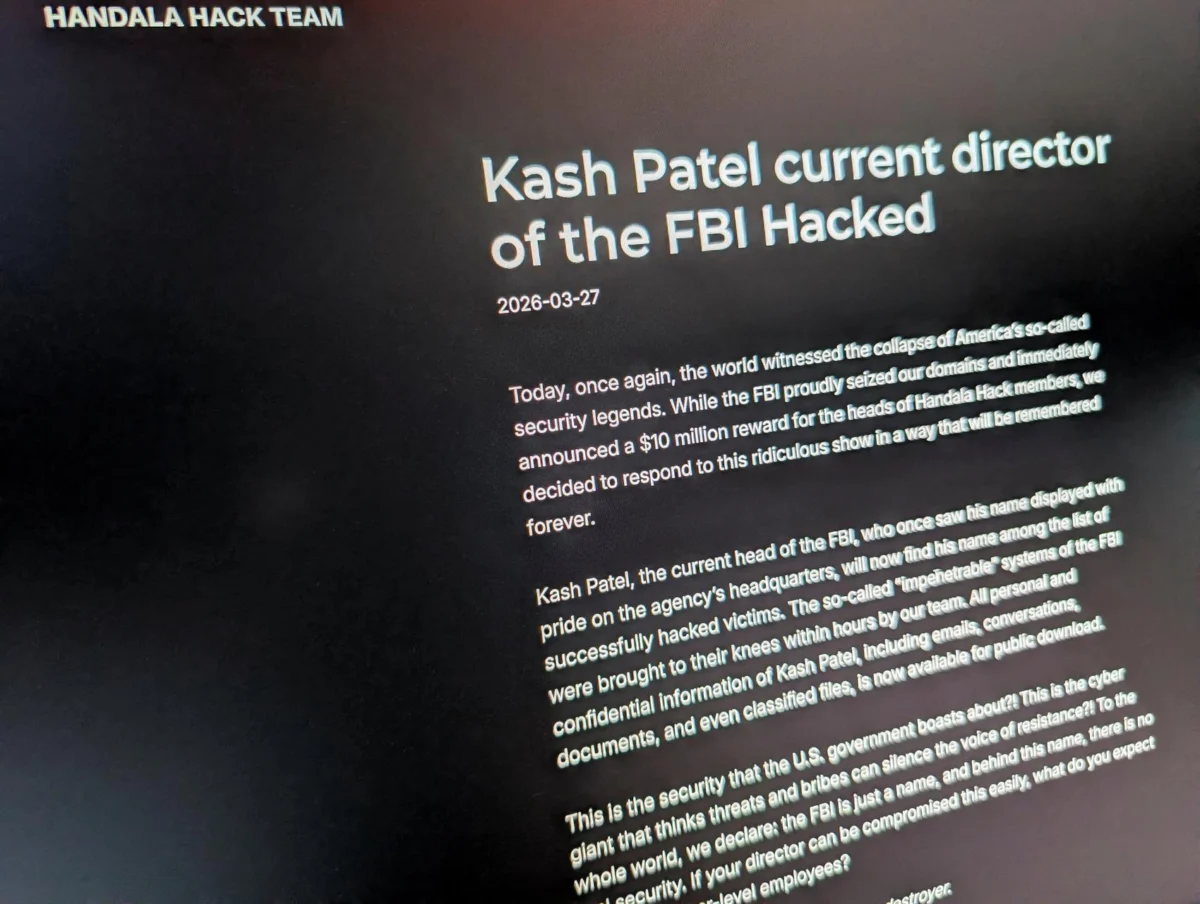
In a bold cyber intrusion, hackers identified as being linked to Iran have successfully breached the personal email account of FBI Director Kash Patel, subsequently releasing a cache of his private photographs and correspondence onto the internet. The breach, confirmed by both the hacking group and the Federal Bureau of Investigation, has drawn attention to the escalating cyber warfare tactics employed by state-sponsored actors and their proxies.
The group, calling themselves the Handala Hack Team, announced their successful infiltration on their website, declaring that Patel would now join a growing list of “successfully hacked victims.” Their online pronouncements were accompanied by the publication of a series of candid personal photographs depicting Patel. These images captured him enjoying cigars, posing in an vintage convertible, and making a humorous face while taking a mirror selfie with a substantial bottle of rum prominently displayed. The nature of these released images suggests a deliberate attempt to humiliate and undermine the public image of a high-ranking U.S. law enforcement official.
Responding to the incident, the FBI acknowledged that Patel’s personal emails had indeed been targeted. A spokesperson for the bureau, Ben Williamson, issued a statement to the press, assuring the public that “all necessary steps to mitigate potential risks associated with this activity” had been implemented. Williamson further emphasized that the compromised data was “historical in nature and involves no government information,” an assertion aimed at downplaying the potential national security implications of the breach.
The Handala Hack Team, which outwardly presents itself as a pro-Palestinian vigilante hacking collective, is widely regarded by Western intelligence and cybersecurity researchers as a front or persona utilized by Iranian government cyber intelligence units. This assessment stems from a pattern of alleged cyber operations that align with Iran’s geopolitical interests and its ongoing digital campaigns. The group’s recent activities include a claimed hack of Stryker, a prominent medical devices and services provider based in Michigan, which occurred on March 11. In that incident, Handala asserted that they had deleted a vast quantity of company data, highlighting their capacity for disruptive attacks against critical infrastructure and corporate entities.
Beyond the release of personal photographs, the hackers also disseminated a selection of over 300 emails allegedly retrieved from Patel’s account. These communications appear to represent a mixture of personal and professional exchanges, with timestamps indicating they date back to the period between 2010 and 2019. The content of these emails, if authenticated, could offer insights into Patel’s professional life and personal relationships during that timeframe, further amplifying the impact of the breach.
While Reuters, the news agency reporting on the incident, stated that it could not independently verify the authenticity of the leaked Patel messages, a crucial detail emerged regarding the email address. The personal Gmail address that Handala claims to have compromised was found to match an address previously linked to Patel in data breaches cataloged by District 4 Labs, a dark web intelligence firm. This connection lends a degree of credibility to the hackers’ claims, suggesting a potential vulnerability that was exploited. Alphabet-owned Google, the parent company of Gmail, did not immediately respond to requests for comment regarding the alleged breach of its platform.
Strategic Vulnerability and Psychological Warfare
The cyber operations undertaken by Iran-linked hackers have become increasingly prominent and boastful, particularly in the wake of coordinated strikes launched by the United States and Israel against the Islamic Republic in the preceding month. Following an initial period of relative quiet, these groups have escalated their public declarations of cyber achievements as the geopolitical conflict continues to unfold.
The Handala Hack Team’s recent activities extend beyond the breach of Patel’s personal account. On Thursday, the group also claimed responsibility for publishing the personal data of numerous employees of Lockheed Martin, a major defense contractor, who are stationed in the Middle East. In response to these reports, Lockheed Martin issued a statement acknowledging awareness of the situation and affirming that the company has robust policies and procedures in place “to mitigate cyber threats to our business.”
Gil Messing, chief of staff at the Israeli cybersecurity firm Check Point, offered an analysis of the hack-and-leak operation against Patel, characterizing it as a deliberate component of Iran’s broader strategy to embarrass U.S. officials and instill a sense of vulnerability. “The Iranians,” Messing stated, “are ‘firing whatever they have,’ indicating a broad, opportunistic approach to cyber attacks designed to maximize psychological impact and sow discord.”
The targeting of personal email accounts belonging to senior government officials is not an uncommon tactic in the realm of international cyber espionage. Breaches and subsequent leaks of such sensitive information have occurred periodically throughout recent history. A notable precedent was the hacking of Hillary Clinton’s campaign chairman, John Podesta’s, personal Gmail account in the lead-up to the 2016 U.S. presidential election, with a significant portion of the data subsequently published by WikiLeaks. In a similar vein, in 2015, teenage hackers managed to penetrate the personal AOL account of then-CIA Director John Brennan, releasing data pertaining to U.S. intelligence officials.
The nature of the breach against Patel, described as “relatively unsophisticated,” aligns with intelligence assessments reviewed by Reuters in early March. These assessments suggested that Iran and its proxy groups might resort to low-level cyber attacks targeting U.S. digital networks in response to significant geopolitical events, such as the killing of Iranian Supreme Leader Ayatollah Ali Khamenei. This suggests a strategic decision to employ asymmetric warfare through cyberspace when direct confrontation is not feasible or desirable.
The potential for further disclosures of compromised data remains a significant concern. Iran-linked hackers may possess additional troves of sensitive information, held in reserve for future strategic releases. This possibility was hinted at last year when another hacking group, operating under the pseudonym “Robert,” informed Reuters of their consideration to disclose approximately 100 gigabytes of data allegedly stolen from individuals close to former U.S. President Donald Trump, including White House chief of staff Susie Wiles. While Reuters was unable to independently verify this claim, and the group has since ceased communication, it underscores the ongoing threat of large-scale data exfiltration and potential blackmail operations orchestrated by state-sponsored cyber actors.
The escalating cyber confrontations highlight a new frontier in geopolitical conflict, where digital vulnerabilities are exploited for political leverage, reputational damage, and psychological impact. As nations continue to invest in both offensive and defensive cyber capabilities, the landscape of international relations is increasingly shaped by the silent, yet potent, battles waged in the digital realm. The release of personal information, particularly of high-profile individuals, serves as a stark reminder of the pervasive reach of cyber threats and the constant need for vigilance in protecting both personal and governmental digital security.
© Thomson Reuters 2026.